I'm not here to take a dump on the hard working web designers who brought their ideas to life because there are good things, and things that need just a smidgen of improvement.
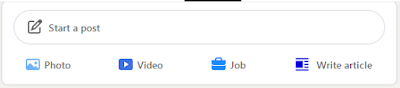
One day in November 2020, I opened my LinkedIn to see this:
Pictured: Rendition of me opening Linked In to see the layout change, but the phone is a laptop, my pillows have Pokemon covers on them, and I am a black woman.
A positive: While it is bright, the icons are not sending me to primary color hell. I call it "Fischer-Price-ification" on Twitter, where major tech companies like Google are changing icons to be very bright, childish colors.
It changes on occasion. I like the Easter and Halloween ones!
Feedback: It's SO bright. It almost overwhelms the icons, especially the "Job" one. Let's give it a change.
I see why Google and Microsoft lean toward those color schemes.
This might be a great opportunity to give us themes.
There needs to be starker contrast between the colors of each icon.
Feedback: The background...the grey. It does not contrast enough.
Too intense.
Better.
You can change the button, but it shares the same properties as the IN logo up there and inline links
A positive:
I like the additions of more rounded edges. As far as I remember (and I could be faulty), they were limited to the Activity section, and the "⬆ New Posts" one was the most prominent.
A positive: I like how the icons change depending on where you are!
(The gif is about 28 second long)
Overall, it's more based upon aesthetics than a total reworking of the website, as far as I can tell.












Comments
Post a Comment