Less 'introduction' and more "Well, I paid and studied to take the CCNA, so I'm going to put this information to use somehow."
Also, apparently network administrators feel very strongly about their routing protocol of choice, and will fight people over it.
So, what is a Routing Protocol?
Routing protocols do a lot of the configuring for you on a network. No need for incessantly typing in static routes, which don't scale easily across a large network and take up a lot of time.
Distance Vector -
Link State -
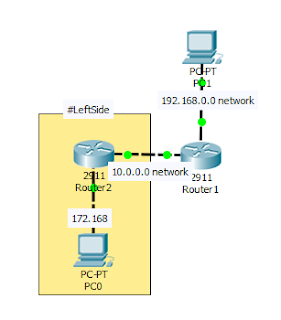
Here is the topology so far; The following configurations are focused on the highlighted bits.
Configuration is simple:
I don't recall version 1 being used...a ton - or at all in the learning present day - so we're going with version 2.
Everything in the 192.168 and 10 networks are being advertised to Router 2 (on the left).
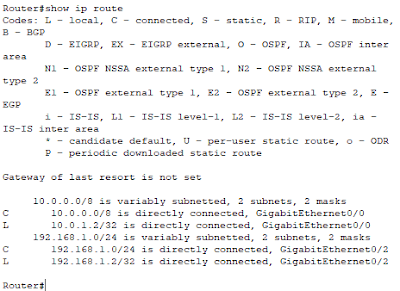
show ip route
The 10 and 192.168.1 networks are 'directly connected', as they're on the same router where I ran the command.
Let's set up Router 2 (on the left) and show ip route again on router 1.
The highlighted area says "Yes, we're connected with the RIP routing protocol.". We can also stop the PCs from receiving RIP updates with the passive-interface command within the routing protocol configuration:
passive-interface [int]
This network is small, so the 15 hop count limit that plagues RIP will be no issue here. But what if the network was far bigger?
Keep reading.
Also, apparently network administrators feel very strongly about their routing protocol of choice, and will fight people over it.
To be clear, I'm 🤔 at the person who went through all that effort to make an account to do this. I have that kind of time as well, but I'm not doing that, I'm doing this.Lol. Someone just created a new Twitter account to criticize my view on BGP. Classy! That’s a quick block. pic.twitter.com/WmoIbqunoI— Daniel Dib (@danieldibswe) November 18, 2019
So, what is a Routing Protocol?
Graphic Design in My Passion
Routing protocols do a lot of the configuring for you on a network. No need for incessantly typing in static routes, which don't scale easily across a large network and take up a lot of time.
Distance Vector -
- How far away is the destination. This is usually counted via hops.
- Slower convergence because it sends the entire routing table.
- Prone to loops.
Link State -
- The router knows about every other router and it's, well, link state.
- The only information that is sent or received is changes in links - are they up or down?
- Converge much quicker, at the cost of using more CPU.
- Has three tables:
- Neighbor - "Who's running the same routing protocol?"
- Topology - "Where is everybody?"
- Routing -"How can I get to this place quickest?"
Here is the topology so far; The following configurations are focused on the highlighted bits.
Configuration is simple:
I don't recall version 1 being used...a ton - or at all in the learning present day - so we're going with version 2.
Everything in the 192.168 and 10 networks are being advertised to Router 2 (on the left).
show ip route
The 10 and 192.168.1 networks are 'directly connected', as they're on the same router where I ran the command.
Let's set up Router 2 (on the left) and show ip route again on router 1.
The highlighted area says "Yes, we're connected with the RIP routing protocol.". We can also stop the PCs from receiving RIP updates with the passive-interface command within the routing protocol configuration:
passive-interface [int]
This network is small, so the 15 hop count limit that plagues RIP will be no issue here. But what if the network was far bigger?
Keep reading.






Comments
Post a Comment