Remember - Your domain (if you're a single person using this) is more than likely COMPUTERNAME\LoginName. It's how you log in on the (local) web portal.
Scan your network within an IP range. If you leave the settings as they are, chances are you're scanning for about 75k IP addresses - and SolarWinds will let you know!
Welcome to the dashboard:
(I can show you the IP addresses because they're local to my network and not public for internet consumption!)
There's a very early 2000s feel which I kind of adore.
Scanning the network did not put my phone 'on the map'. I put in my phone's IP address to see if it could be found. They're on the same network. This nifty screen popped up with how I can monitor myself!
I removed the Active Directory option.
(Remember, this is the range of private IP addresses.)
I can set up an email alert if the phone fails.
Here are all of the devices being managed...all 2 of them.
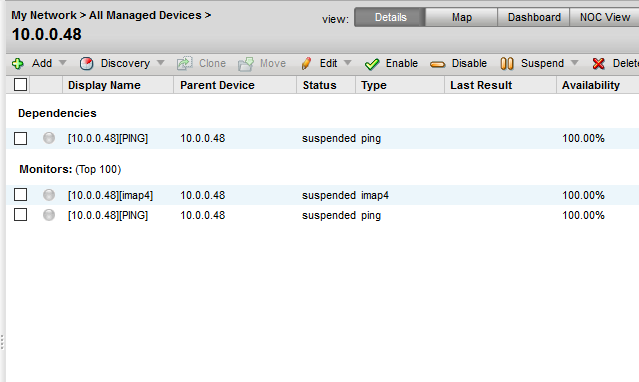
A closer look at the phone:
The status is suspended...what does that mean in this context? Well, that's when we hit 'help' in the upper right hand corner and are taken to the online guide.
There's that 2000s style again!
When my phone times out, ipMonitor catches it;
And here is a snazzier (partial) view on what is being monitored on the phone.
While the scanner did not pick up on many network devices, I consider that something I did. Suspicions involve Xfinity router preventing a ping sweep. It would probably act accordingly if you were using this with enterprise level equipment.
Putting in my phone's IP address was easy, and it was seen and able to be monitored quickly.
As this is only a demo with a limited network, so far, this is the gist of it.
EMPLOYERS: Find things, use things. This shows adaptability (scan doesn't work? Put it in manually), learning, and documentation.








Comments
Post a Comment